My New Book is Here: The Agentic SOC: Architecting the Autonomous Security Operations Center for the Post-Human Threat Landscape
Front Cover
Back Cover
The Human Era of Cybersecurity is Over. Welcome to the Post-Human Threat Landscape.
I still remember the days when a well-configured firewall and a solid signature-based antivirus were enough to let a Chief Information Security Officer sleep through the night. If you were breached, it was usually because a human on the other side of the globe found a clever exploit and manually typed their way into your network. It was a game of chess—human versus human.
I am here to tell you that the chessboard has been flipped. The opponent is no longer human, and they are no longer playing by our rules.
I am incredibly excited (and, frankly, a little terrified) to announce the release of my brand new book: The Agentic SOC: Architecting the Autonomous Security Operations Center for the Post-Human Threat Landscape. This isn’t just another cybersecurity manual. It is a survival guide for the next decade of digital warfare.
Why the Legacy SOC is Dead
For years, we have thrown human analysts at the problem of cyber defense. We built massive Security Operations Centers (SOCs), deployed reactive SIEMs, and wrote static playbooks. But as I dive into in the opening chapters of the book, this model is now a mathematical impossibility.
Why? Because of the weaponization of Artificial Intelligence. Here is a sneak peek straight from the first chapter of the book:
“The true inflection point, however, was not organization, but cognition. The strategic decision by nation-state actors to weaponize artificial intelligence has irrevocably altered the physics of cyber warfare. State-sponsored research programs, fueled by budgets rivaling military hardware development, have produced offensive AI models capable of operating with a speed, scale, and stealth that defies human comprehension.”
You cannot fight compute-speed attacks with human-speed triage. It is an asymmetric slaughter. To survive, we have to fundamentally rethink the architecture of defense.
Enter the Agentic SOC
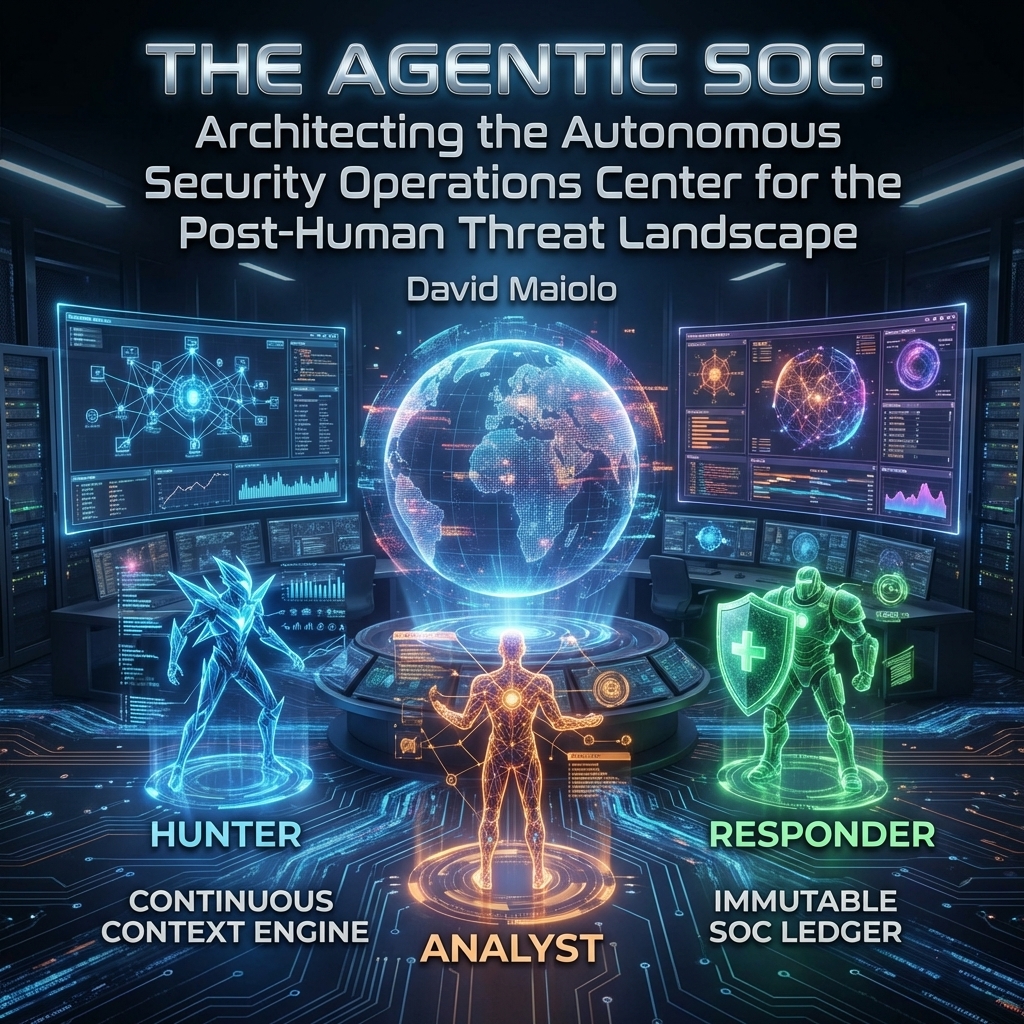
In The Agentic SOC, I guide you through the death of legacy systems and introduce you to the new defenders of your digital perimeter: autonomous, goal-oriented AI agents. We are moving from a world where AI simply flags anomalies for humans to review, to a world where AI acts.
I break down the engineering of three specialized AI personas powered by advanced Large and Small Language Models (LLMs and SLMs):
- The Hunter: An autonomous sentinel that proactively scours your network context, utilizing semantic search to find latent threats before they execute.
- The Analyst: A cognitive engine that ingests massive data streams, correlates complex attack vectors, and determines the exact nature of the breach without human fatigue.
- The Responder: The execution arm that leverages secure infrastructure APIs to isolate endpoints, sever malicious connections, and neutralize threats at the speed of compute.
The Terrifying Paradox of Modern Cyber Warfare
One of the core themes I explore in the book is how AI has completely democratized destruction. You used to need a team of elite hackers to breach a Fortune 500 company. Not anymore. As I wrote in the text:
“This shift has created a terrifying paradox: as the sophistication of the attack has reached unprecedented heights, the barrier to entry for executing such an attack has collapsed. The bespoke tools once locked away in the digital vaults of intelligence agencies are now being refined, packaged, and democratized through AI.”
To help visualize this, I’ve included a comprehensive breakdown in the book that maps out how we got here. Here is an adapted look at the evolution of the adversary:
| Attribute | Era 1: The Hobbyist (1990s-2000s) | Era 2: The Syndicate (2000s-2020s) | Era 3: The Agentic State (Present) |
|---|---|---|---|
| Primary Actor | Individual / “Script Kiddie” | Organized Crime / Hacktivist Groups | Nation-State / AI-Proxy |
| Core Tactic | Manual exploit, website defacement, simple viruses. | Ransomware-as-a-Service, large-scale data theft, DDoS for hire. | Autonomous reconnaissance, AI-generated polymorphic malware, adaptive lateral movement. |
| Required Skill | Low to moderate; ability to run pre-made scripts. | High; deep knowledge of network architecture, programming, and operations. | Low; access to a powerful offensive AI model is sufficient. The model possesses the skill. |
| Speed of Attack | Human speed (minutes to hours). | Human-led, tool-assisted (seconds to minutes). | Compute speed (milliseconds to microseconds). |
| Defense Paradigm | Firewalls, Signature-based Antivirus. | SIEM, IoC/TTP correlation, human-led threat hunting. | Autonomous Agents, behavioral heuristics, self-healing infrastructure. |
Are Humans Obsolete?
When I talk about an autonomous SOC, the first question I always get is: “David, are you telling me to fire my security analysts?”
Absolutely not. But their job descriptions must change today. In the book, I dedicate significant time to Governance, Risk, and Compliance (GRC) and the frameworks of Human-in-the-Loop (HITL) and Human-on-the-Loop (HOTL). We are not erasing the human element; we are elevating the overwhelmed analyst into a strategic AI supervisor. Your team will stop drowning in false positives and start directing the overarching strategy of your defensive swarm.
Because the reality of the situation is stark. As I sum it up in Chapter 1:
“We are no longer defending against human adversaries who think, type, and strategize in human time. We are defending against algorithms that can test millions of exploit variations in the time it takes a human analyst to read an alert notification.”
Building the Fortress
If you’ve followed my previous work, such as The Zero-Trust AI Enterprise: Architecting Secure, Private, and Compliant Large Language Models for the Fortune 500 or my foundational guides like Modern Cloud Security Architecture – Volume 1: Compliance Frameworks, Risk Management, and Foundational Design Principles, you know that I don’t deal in high-level fluff. I write for the builders, the architects, and the engineers.
Just like I mapped out the shift from deterministic coding to probabilistic systems in Full-Stack AI Engineering: Architecting Production-Ready Agents, Advanced RAG, and Privacy-First Local LLMs, this new book gives you the exact, actionable blueprints to deploy multi-agent collaboration, dynamic containment, and self-healing networks.
The arms race of autonomous offense versus autonomous defense has already begun. You cannot afford to fight the wars of tomorrow with the tools of yesterday.
Ready to architect your defense?
Join me on this journey and future-proof your corporate ecosystem. Secure your copy today:
Buy The Agentic SOC on Amazon Now
Stay secure, stay ahead, and I’ll see you on the digital frontlines.
— David Maiolo

Leave a Reply
Want to join the discussion?Feel free to contribute!